VMware Server 1.0.x
ssh -4 -v -L 1902:127.0.0.1:902 vmwareserver1.example.com
[messages resulting from -v option removed]
debug1: Local connections to LOCALHOST:1902 forwarded to remote address 127.0.0.1:902
debug1: Local forwarding listening on 127.0.0.1 port 1902.
ssh -v shows that all connections to local loopback address 127.0.0.1 and TCP port 1902 are forwarded over ssh to the server's loopback address 127.0.0.1 and port 902.
The reason I am using port 1902 at the local end is that in order to use port 902 ssh must run as root.
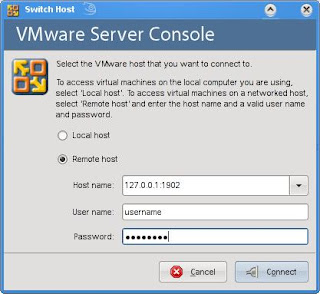
Connecting to the server with WMware Server Console is done by choosing "Remote host" and entering 127.0.0.1:1902 as "Host name".
VMware Server 2.0.x
ssh -L 1902:localhost:1902 -L 8333:localhost:8333 vmwareserver2.example.com
The difference with 1.0.x is that:
- Two ports are forwarded now: also port 8333 is forwarded to the remote server
- Local port 1902 as now forwarded to remote port 1902, not to port 902
VMware Server 2.0.x uses two ports for management:
- Port 8333 is used with web browser for initially contacting the server over https
- The number of second port is learned from connection 1, which in this case is 1902
If the server has already been configured to use port 902 and reconfiguring is not an easy option, the ssh command can be run e.g., with sudo as root with port set to 902.
In both cases, once the two ports (8333 and 1902 or 902) have been forwarded with ssh, the server can be contacted with the web browser using https://127.0.0.1:8333/
Tricky, isn't it?
No comments:
Post a Comment