Friday, November 3, 2017
What does Arch Red do?
The Radiator products and services have become our primary focus and business. We have developed Radiator further, designed and implemented features, which make it even more suitable for operator and carrier use. This year we released our new NFV compatible Radiator product, Radiator VNF and have released already the second minor version (2017.1) of it. If you are interested about what Radiator VNF does, you should check this Good News from Finland article about us or see our Radiator VNF video in Youtube.
We do not post a lot to this Arch Red blog anymore, but you can find far more material and things what we do from our Radiator Cookbook blog.
Tuesday, December 1, 2015
verkkovieras.fi -- making enterprise Wi-Fi authentication easy
verkkovieras.fi for simple and secure federated Wi-Fi authentication
 |
| security by David Bleasdale |
Verkkovieras is a Finnish word, which means network guest. Verkkovieras.fi is our cloud authentication service for organisation’s employee and guest network access control. The service also supports authentication roaming federations such as eduroam and roam.fi making the service an easy way to deploy and serve federated network access for employees, guests and partners.
We know that maintaining user databases and RADIUS servers for employee and guest access can be difficult, especially when there’s additional complexity such as federated roaming. With verkkovieras.fi we focused in building a service, which is easy to deploy and easy to use. We thought, designed, thought some more and improved our design to be as clean and clear as possible.
Easily deployed in any Wi-Fi network
To deploy verkkovieras.fi authenticaton service you only need RADIUS capable authenticated devices such as for example almost all Wi-Fi controllers and access points. The authenticating device, usually the Wi-Fi controller, needs to be able to communicate with our cloud based servers in Internet and that’s it -- only our server details and Wi-Fi networks need to be configured in the controller.User account registration as easy as email
 |
| verkkovieras.fi registration screen in Finnish |
Federated roaming with a flick of a switch
Roaming federations and federated user access is even simpler, just select which federations and to activate or deactivate it. Your employees or visiting roaming guests are then able to roam free within federations and networks with same profiles they use for network access in your home network.
Easy guest user access or traditional vouchers -- you choose
 |
| Howard Lake: Sainsburys Active Kids vouchers |
For guest user access there are two options, a simple time-limited guest user account for automated access and possibility to create and print more traditional time-limited guest user accounts before hand. Automated access means that the user account can be integrated for example with WWW page based authentication to provide guest short Internet access with just a click of a button on the authentication page. The traditional guest user accounts can be used like vouchers, the username and password must be entered on the authentication page or system dialog to get the access to network.
All this as a cloud service, ready to be deployed today
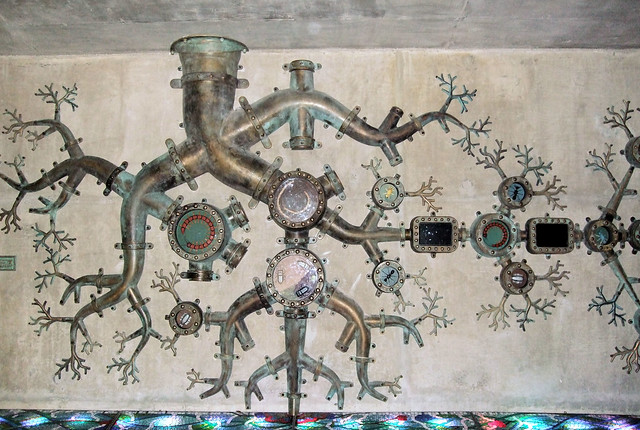
 |
| verkkovieras.fi architecture |
We packaged all this in a redundant Amazon cloud based service distributed across two geographical regions, where we handle the difficult details such as scaling, server certificates, EAP methods (EAP-PEAP, EAP-TTLS, EAP-PWD) leaving you as a customer time to focus to your business and core functions.
If you are interested, contact Arch Red sales ( sales <at> archred.com ) for more details.
Tuesday, May 26, 2015
New blog about Radiator: Radiator Cookbook
Wednesday, August 6, 2014
What does Internet of Things mean for service providers?
Industry experts, vendors and conference organisers around the world are hyping about Internet of Things (IoT) and even more specific things such as Industrial Internet, but what does it all mean for network service providers, operators and enterprises?
To find answers to that question we must first select our viewpoint. In this blog post, we look IoT from the perspective of network service provider, for example, operator, enterprise or industrial IT department. Let us start by looking first at the graph drafted accordingly to Gartner, IDC, Strategy Analytics, Machina Research, company filings and Business Insider Intelligence estimates.
- managing and provisioning configurations to the ever growing variety of devices
- defining, creating and configuring subscriptions and subscription parameters to the ever growing variety of customers and devices
- handling security configurations in multi-service provider environment, separating service providers and networks from each other
- federating identity management instead of providing a single source identity management
- scaling the authentication, authorisation and accounting (AAA) infrastructure from single identity provider model to multiple identity providers model
- coping with multi-access (WiFi, LTE, 3G, 2G), multi-homing devices and their AAA
- connecting services and AAA with various IoT service providers
- utilising and favouring open standard APIs, protocols and interfaces
- measuring and monitoring everything
- automating everything (for example, service/subscription provisioning, configuration provisioning, security, identity federation)
Decisions cannot be made without data. Measuring and monitoring the infrastructure, network, devices, sensors and nodes makes it possible to gather data about current situation. Measured data is used for historical or future trend analysis. Based on the data and/or analysis, automated decisions can be made and provisioned to the infrastructure components utilising standard interfaces and protocols.
By combining these three approaches, the objective for service providers is to do for the Internet service production the same that has already been done by automation in the factories -- automate as much of the actual production as possible, monitor and measure to gather data and make informed, even automated decisions based on the data.
Tuesday, July 8, 2014
There is no Free Wi-Fi, but there can be Sustainable Wi-Fi

Today Engadget reported that Free WiFi provider admits to making up 90 percent of its revenues. The company, Gowex, runs networks in 85 cities around the world (according to company WWW pages) offices in Madrid, Paris, London, Buenos Aires and Shanghai. The company claimed that it had developed a sustainable business model for free Wi-Fi based on the idea that company makes its revenues from partnerships with local governments, carriers with Wi-Fi offloading and from premium fees (i.e. selling premium user accounts).
Some may view this as a proof that Gowex's business idea and model did not work, but I would not claim that without looking into if they managed to get any revenues at all. Running company badly and falsifying revenues and accounting are very different things from the actual business idea and model not working. I actually think that those ideas from where Gowex planned to get revenues are valid ones and they seem to have made real roaming deals with roaming brokers such as iPass, Boingo etc. These revenues could then be used to subsidise the service costs of running WiFi networks or related services, but naturally the company should get more revenues from the service it provides than the costs of producing it. And that is actually why I do not believe Free Wi-Fi exists.

The Free Wi-Fi is an illusion for consumers. Somebody always ends up with the bill. It may be the company, organisation or city providing or buying the Free Wi-Fi service out of hospitability. It may be an airport or a shopping mall deploying or buying a service for tracking customer movements or web surfing, but like many other free Internet services, Free Wi-Fi is not really free. You as a consumer may think that with Free Wi-Fi that you are still customer, but the reality is that the one providing and paying for Free Wi-Fi service, needs to get enough benefits and/or revenue from providing the free service to you and their benefit maybe the data about you.
Where Gowex was on a right is that providing Wi-Fi for free needs to be sustainable. The Wi-Fi network service needs to provide so much benefits for the one paying for it, that the payer is willing to cover the costs of running, maintaining and developing the network. Too often in many hospitability guest networks (hotel/conference Wi-Fi, company guest Wi-Fi) the deployed network may serve its users when it was first deployed, but the development of it (Internet bandwidth capacity, better radios) is neglected until enough users are complaining about it. In city-wide Wi-Fi networks similar kind of problems occur, when city-wide Wi-Fi is setup with development project money from government or EU without any plan how to cover the costs after the development project has ended.
Sustainable Wi-Fi networks should be planned so that they can be maintained and even developed with the revenues coming from organisations and companies benefitting from the network service, or from something measurable the network provides. There even exists a successful example of this kind of sustainable global Wi-Fi network concept -- eduroam (*).
In eduroam, universities, research institutions, government organisations and even cities have seen the benefits of joining their existing Wi-Fi networks via federated RADIUS authentication and providing this way a free Wi-Fi around the world for researchers, teachers and students. Every organisation deploys, maintains and develops their own network service with their own funding and shares it with the other eduroam organisations. There is no single vendor, service provider or organisation controlling anything. Instead, every vendor, service provider or organisation which is ready to fulfil the open requirements and standard interfaces is welcome to join or provide equipment or services to other eduroam organisations. There are not a lot of revenues or profits moved around, just normal network and authentication business for companies, but the benefits are clear for participants to justify the costs of basically running the Wi-Fi networks, which they are going to do anyway.
eduroam is real, sustainable Wi-Fi and I am hoping that we (Arch Red and Open System Consultants) may help in bringing its benefits also to wider audience in a very near future. eduroam itself still limits its use to universities and research organisations and networks and cannot unfortunately yet be used as a common global concept to provide sustainable Wi-Fi for all.
* eduroam is a registered trademark of TERENA. Arch Red and Open System Consultants are independent of TERENA".
Sunday, April 28, 2013
Australian RADIUS experts and Finnish Internet engineers combine forces
The Finnish Internet engineering company Arch Red Oy expands its global operations by acquiring a controlling interest in Australian software company Open System Constultants Pty Ltd (OSC). OSC's main product Radiator RADIUS server is one of the most comprehensive RADIUS servers on the market. It is a base component for implementing both wireless (WLAN, 3G, 4G) and wired customer authentication solutions, which Arch Red has delivered to its operator and company customers in cooperation with OSC for several years.
Through this cooperation Arch Red gains access to OSC's active resellers in almost 50 countries and direct customer contacts with many operators and an even larger number of enterprises, universities and organisations around the world.
"By combining Arch Red and OSC, we can serve our existing and new customers even more efficiently and comprehensively than before." Arch Red managing director, Karri Huhtanen, explains and continues:
"In addition to developing Radiator further, we will also develop new customer services by offering, for example, ready-to-use RADIUS authentication solutions as subscription based cloud services.For more information, please contact:
- Karri Huhtanen
- managing director, Arch Red Oy
- +358 44 087 6546 www.archred.com
- managing director, Arch Red Oy
Arch Red Oy is a Finnish Internet engineering company, which offers both products and services to service providers for wireless (Wi-Fi, 3G, 4G) user authentication, management and roaming. Arch Red also offers solutions and services for white-label Wi-Fi and community network user and guest authentication.
Open System Consultants Pty Ltd is an Australian software company. Its main product is Radiator RADIUS server software, which has customers in 180 countries and resellers in over 46 countries around the world. Radiator RADIUS server software is used in operator and service provider networks around the world for user authentication, provisioning and configuration management. Radiator RADIUS server is also a central component in deploying Wi-Fi network authentication and when Wi-Fi authentication is connected to the 3G/4G network authentication infrastructure.
Thursday, September 8, 2011
What about CAs in mobile devices?
- Google Online Security: An update on attempted man-in-the-middle attacks
- Operation Black Tulip: Fox IT's report on the DigiNotar breach
- F-Secure blog: DigiNotar hacker comes out
- (Sophos) Naked Security: Microsoft revokes DigiNotar certificates from Windows, Mac users still vulnerable
- (Sophos) Naked Security: Firefox 6.0.2 fixes yet more DigiNotar certificate fallout
One of the generally trusted certificate authorities (DigiNotar) failed to protect its services and was compromised. There now exists DigiNotar signed certificates in the wild free for attackers to use for several online and software update services including companies such as Microsoft, Google and organisations like Mozilla(Firefox). This means that if your operating system or browser certificate stores are not updated, your device is vulnerable to attacks based on these certificates. Attacks can for example install malware on your computer in the form of updates or collect your passwords for various services.But since most of the operating system and browser vendors already reacted and I have installed updates I am now secure, right?
No you are not. While most of the operating system and browser have removed the CA certificate in question we still have a huge number of devices which may have those CA certificates installed -- the mobile devices. I have not yet received an update for my Android phone (Samsung Google Nexus S) and I think it is pretty much the same for all other mobile phone vendors too, Windows Phones, old and new S40, Symbian, Maemo phones and iPhones included. And it does not even stop to mobile phones, nowadays we have already tablets and all kinds of embedded devices, which may have the operating system included certs installed. Our mobile devices continue to be vulnerable to those leaked certificates and in most cases the users cannot even check or do anything to remove the certificates!
One glimmer of hope is that DigiNotar has not perhaps been in all mobile devices' CA certificate storage, but then again we still have Comodo there and now GlobalSign has stopped signing certificates and is checking their systems for intrusion. Another glimmer of hope is that maybe perhaps now industry will take a closer look at the current certificate authority structure and the system will be improved or fixed for example like Moxie Marlinspike suggests.